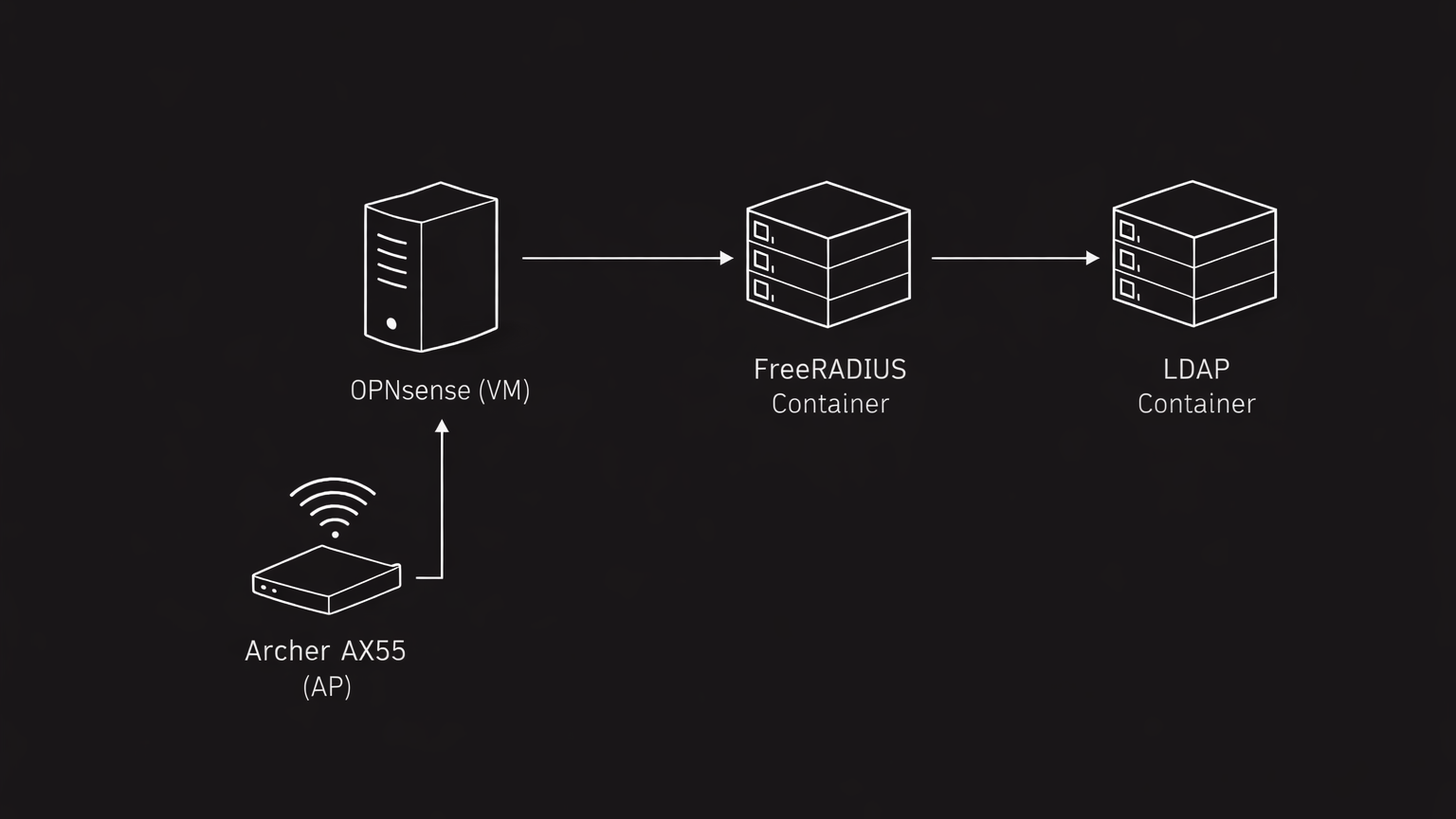
For a while, I’ve wanted to set up a solid Wi-Fi network for devices in my homelab. Instead of just using a simple access point with a shared Wi-Fi password, I decided to go all the way: I implemented per-user authentication with FreeRADIUS and LDAP, giving me fine-grained control over who can connect and what they can access.
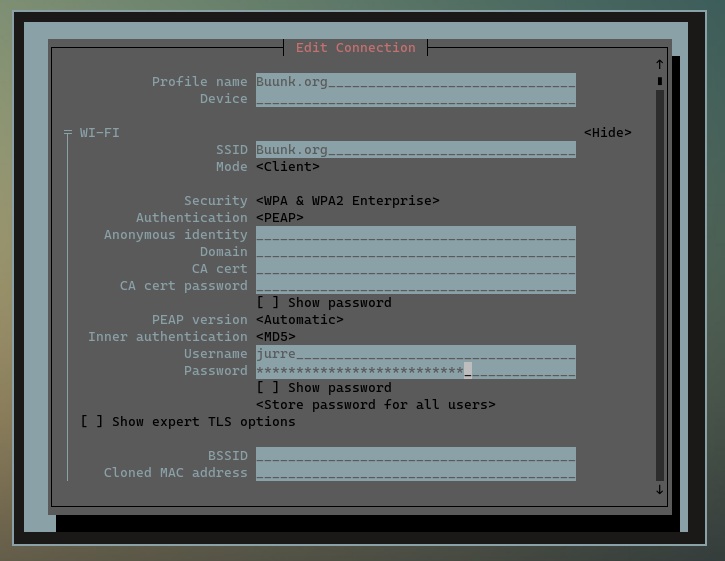
The RADIUS server itself runs in an LXC container on my production cluster, making it fully integrated with my infrastructure. This setup ensures it’s always on, highly available, and easy to maintain. I also ensured that the container has access to my existing LDAP directory (ou=people,dc=buunk,dc=org), so it can verify user credentials and check group membership.
The Archer AX55 is used purely as an access point. It points to my main OPNsense router, which handles DHCP, routing, and forwards RADIUS requests to the FreeRADIUS container. Seeing a client connect for the first time is satisfying: FreeRADIUS looks up the user in LDAP, verifies the password, checks that the user is in the wifi-users group, and grants access.
ldap: User object found at DN "uid=jurre,ou=people,dc=buunk,dc=org"
ldap: Processing memberOf value "cn=wifi-users,ou=groups,dc=buunk,dc=org" as a DN
if (Ldap-Group == "cn=wifi-users,ou=groups,dc=buunk,dc=org") -> TRUE
Reply-Message := "User is in wifi-users group"The group check policy is particularly neat. FreeRADIUS evaluates the check_group policy to ensure the user belongs to wifi-users. This allows me to separate access based on LDAP groups and makes it easy to extend later—for example, to assign VLANs or enforce more granular policies.
Here’s a snippet from that policy:
policy check_group {
if (Ldap-Group == "cn=wifi-users,ou=groups,dc=buunk,dc=org") {
update reply {
Reply-Message := "User is in wifi-users group"
}
}
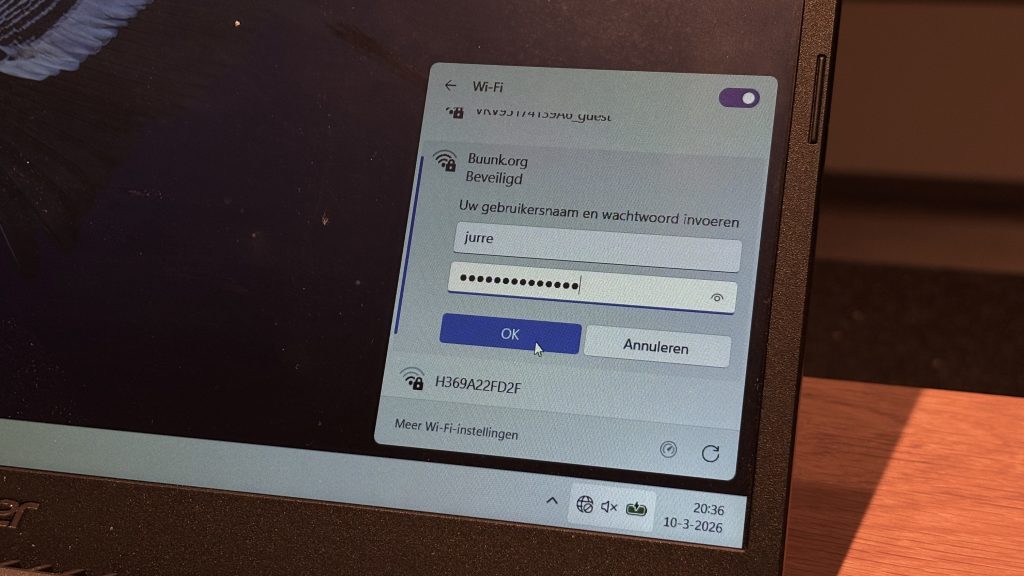
}Clients connect via the AX55, which is configured for WPA2 Enterprise. The OPNsense router handles DHCP and dynamic DNS, and I can watch the logs as authentication occurs. The EAP-PEAP tunnel is established, credentials are verified, and access is granted all while keeping passwords secure.
eap_peap: Session established. Decoding tunneled attributes
eap_peap: Success
eap_peap: Using saved attributes from the original Access-AcceptOverall, this project gave my homelab Wi-Fi access that feels enterprise-grade. By combining my production cluster LXC container running FreeRADIUS, LDAP for user management, OPNsense as the main router, and the Archer AX55 as a managed access point, I now have a secure, auditable, and flexible network.
Next, I plan to experiment with dynamic VLAN assignment based on group membership. This will give me more control over what guest accounts and IoT devices can access. For now, it’s already incredibly satisfying to see per-user authentication working perfectly in my home lab environment.
If you are interested in the technologies used to build this network, here are some links for more information:
FreeRADIUS – RADIUS server for secure authentication: https://freeradius.org
LLDAP – Lightweight LDAP for user and group management: https://github.com/lldap/lldap
OPNsense – Firewall and router: https://opnsense.org
Archer AX55 – Wi-Fi 6 access point: https://www.tp-link.com/en/home-networking/wifi-router/archer-ax55/